Using Azure Active Directory you can provision users in Couchdrop, as well as use to authenticate with the platform.
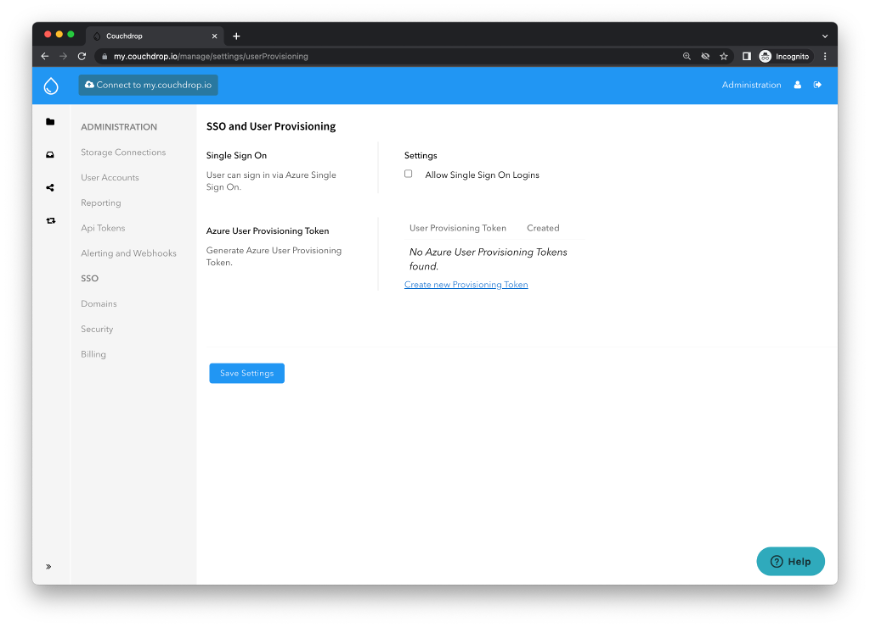
Step 1. Enable SSO and User Provisioning on Couchdrop
Navigate to SSO and User Provisioning in Couchdrop’s interface and create a new Provisioning Token. This will be used in the Azure Active Directory provisioning process.
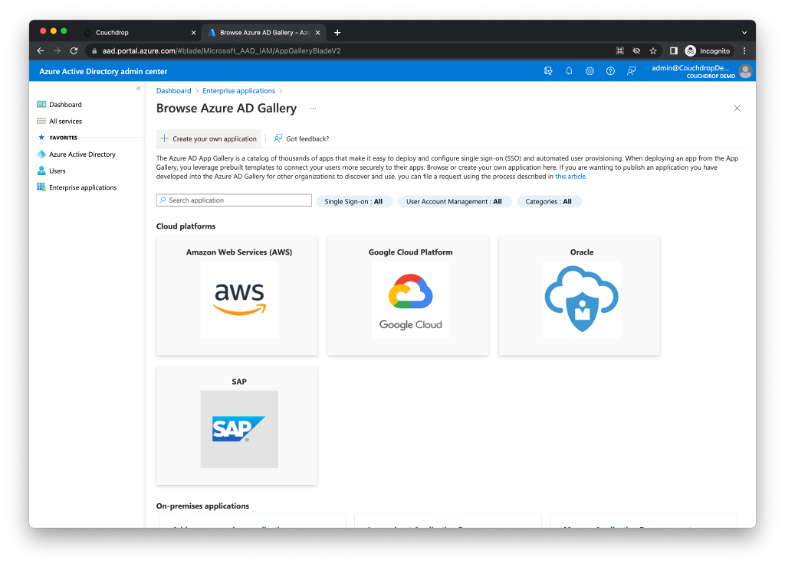
Step 2. Configure Enterprise Application in Azure Active Directory
Navigate to your Administration dashboard in Microsoft’s admin portal and create an enterprise application.
Provide a name for the application and select “Integrate any other application you don’t find in the gallery (Non-gallery)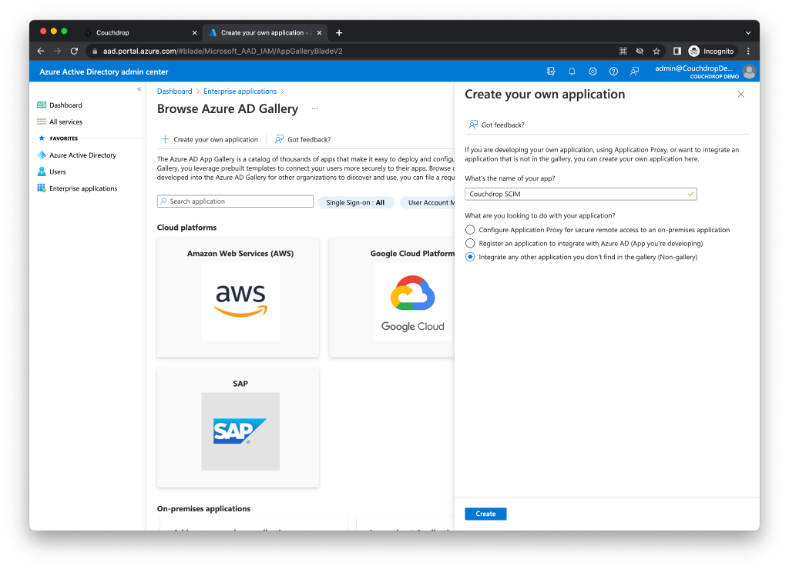
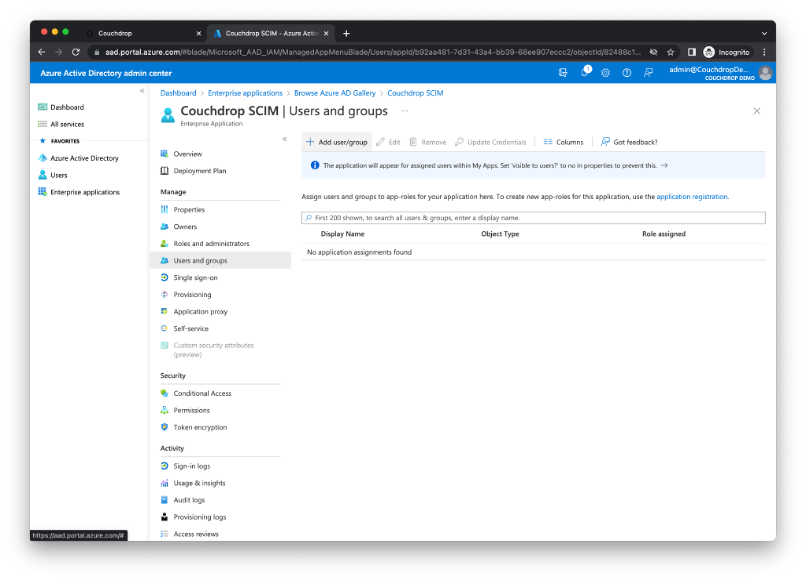
Next assign users and groups to the newly created application that you would like to have provisioned in Couchdrop.
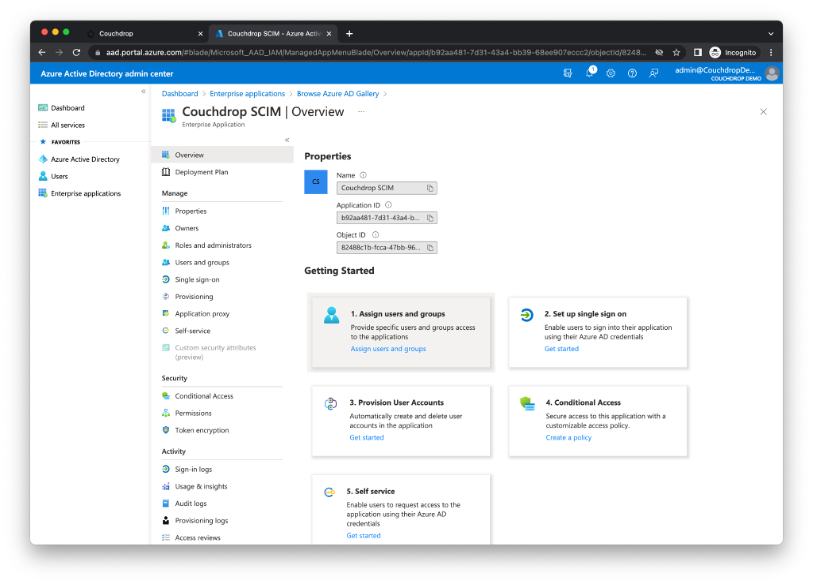
Select Add user/group
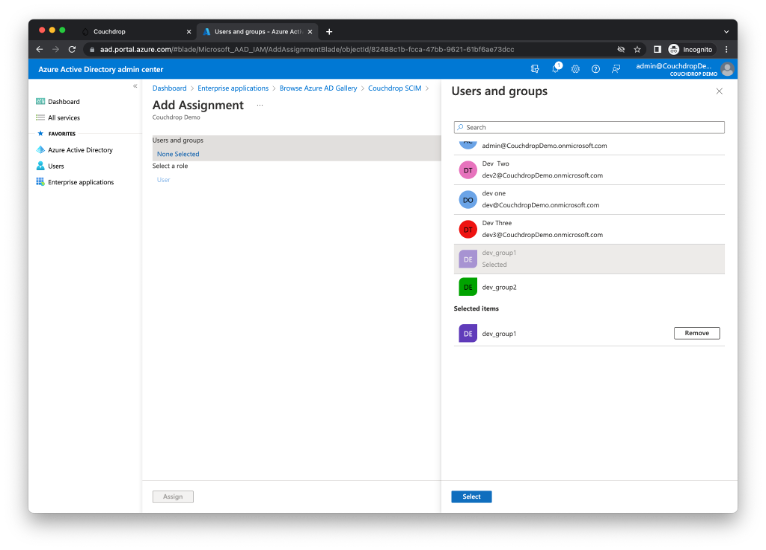
Select the desired users or groups that should be provisioned through to Couchdrop then Select and Assign.
Step 3. Configure SCIM provisioning between Azure Active Directory and Couchdrop
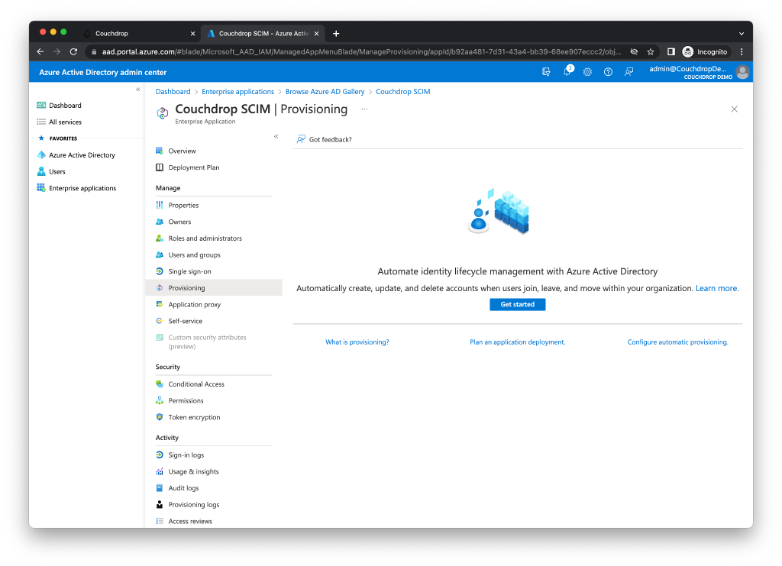
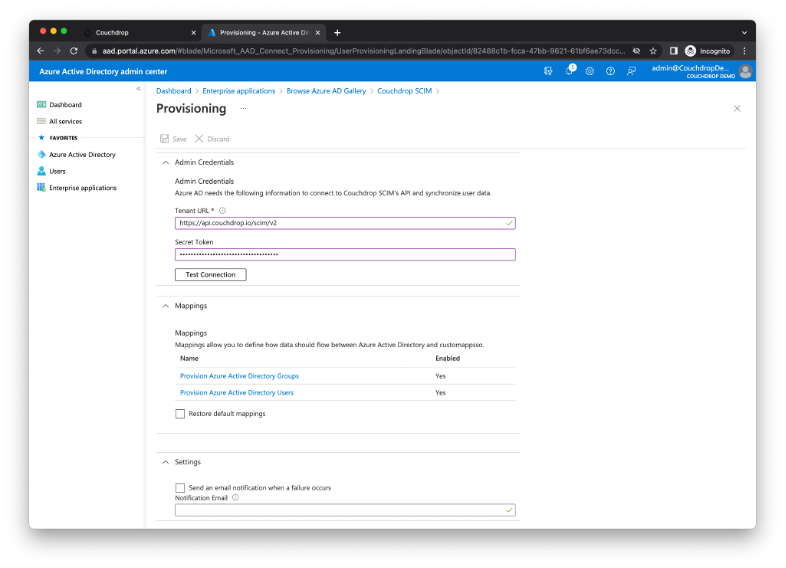
Navigate to the Provisioning Tab on the left hand side. Next select Get started to configure the tenant URL and the User Provisioning Token that was created at Step 1. Provisioning mode should be set to automatic. The Tenant URL is: https://api.couchdrop.io/scim/v2.
Select Test Connection and Azure will attempt to connect as well will retrieve schema information needed for the user and group mapping. If tested successfully then select Save.
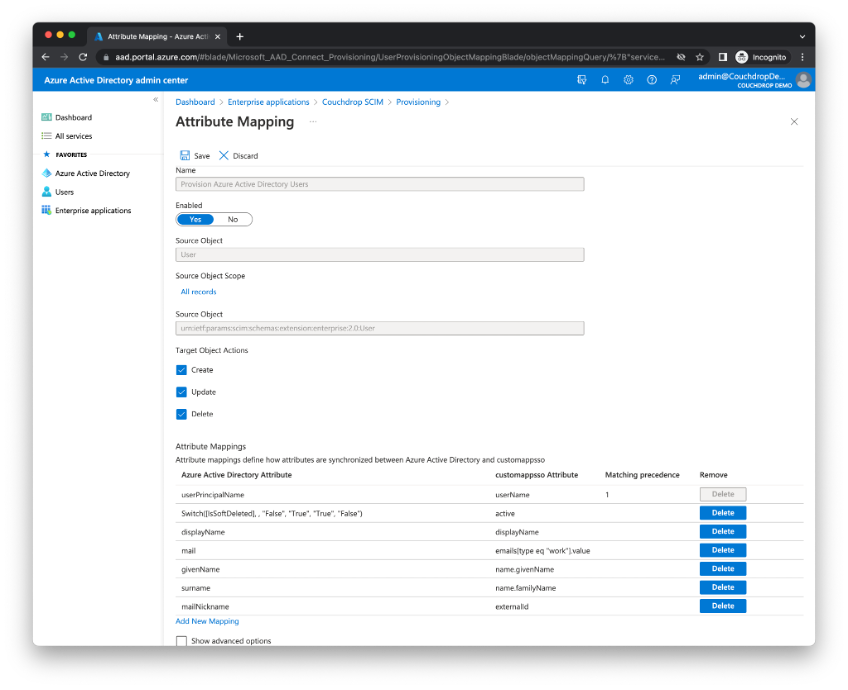
Step 4. Configure user mapping
Select on Provision Azure Active Directory Users as required.
Couchdrop requires the following user SCIM attributes for the SCIM system to be mapped, all others should be removed.
|
Custom Application SSO Attribute |
|
userName |
|
active |
|
emails[type eq "work"].value |
|
name.givenName |
|
name.familyName |
|
externalId |
The externalId attribute may need to be remapped from mailNickname to objectId on the Azure Active Directory attribute side depending on your settings.
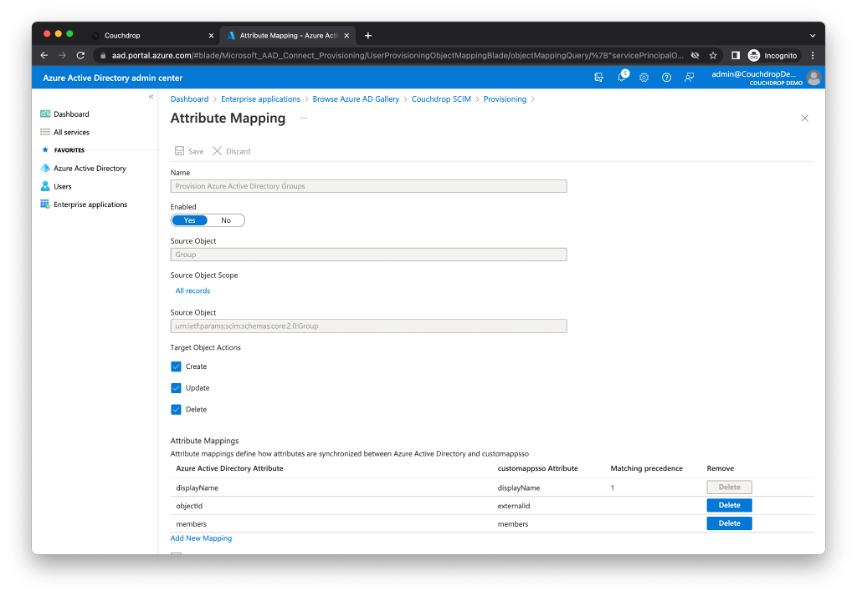
Step 5. Configure group mapping
Select on Provision Azure Active Directory Groups as required.
Couchdrop requires the following user SCIM attributes for the SCIM system to be mapped.
|
Custom Application SSO Attribute |
|
displayName |
|
externalId |
|
members |
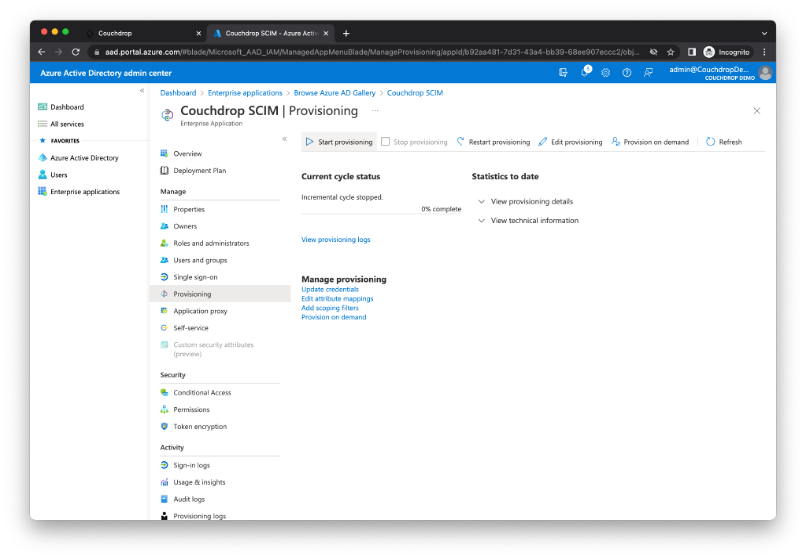
Step 6. Start the user and group provisioning process
Navigate back to the custom application breadcrumb (in this case it’s Couchdrop SCIM) and to Provisioning. From here select the Start provisioning button.
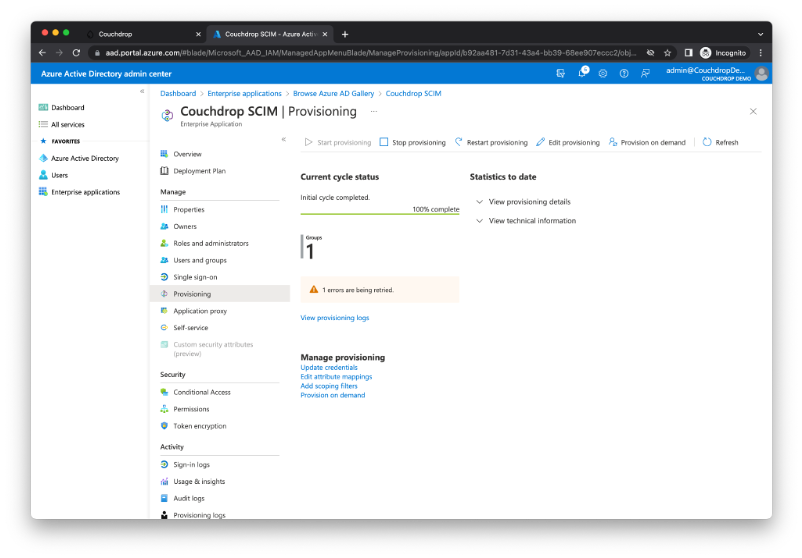
After the provisioning has completed running the first time a status should be required that indicates how many users and groups were provisioned within the Couchdrop product. Further information can be located by selecting View provisioning logs.
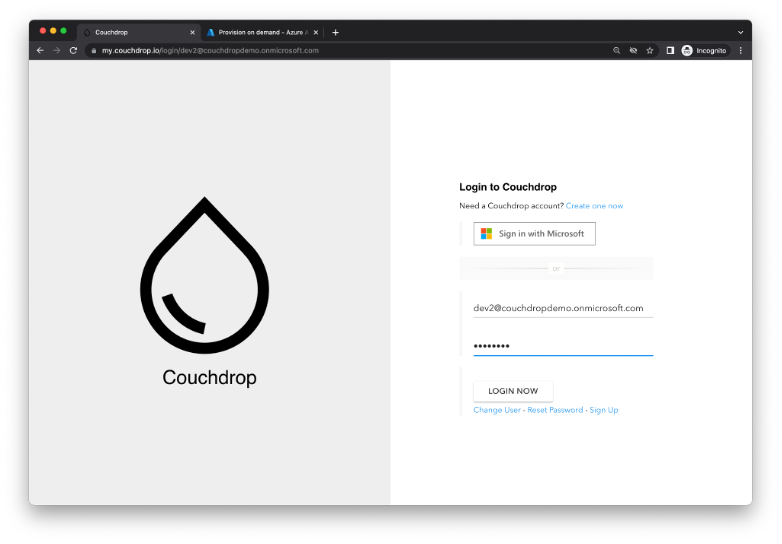
Step 7. Log into Couchdrop using a Microsoft Account
Navigate to your Couchdrop portal and enter in the username of a provisioned account. If this was successful you should see the Sign in with Microsoft button appear, where you can now continue to log in with your MIcrosoft account’s credentials.
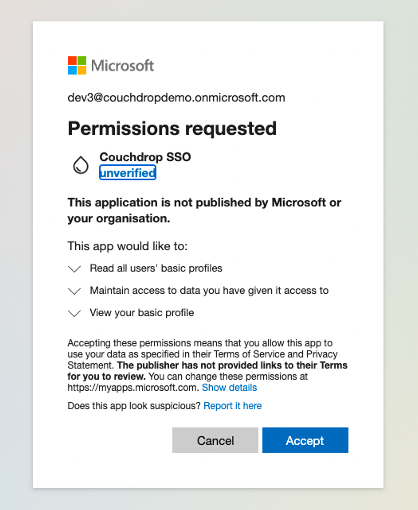
On the initial signing in, Microsoft’s consent screen will appear and ask the user to give permission to sign in.
For any assistance throughout the process please contact support@couchdrop.io